Feature Spotlight
Timeline Tool
See the Life of a Resident
Have you ever wanted to see all of a resident’s communication activity in one place, or when a call happened in relation to a deposit? Now you can. With the Telmate Timeline, we’ve compiled an inmate’s booking, financial, and communication history into a single sortable history. The Telmate Timeline combines all of the following:
- Booking Information Where and when the resident was booked, including booking photo (when available.)
- Export for Trial Exhibits Timelines may be exported as distributable PDF documents or graphic trial exhibits appropriate for printing or emailing.
- Calls Includes both attempted calls and completed call recordings, as well as recipient detail and call duration.
- Voicemail Includes the phone number and verified contact name and identity (with Telmate Verify).
- Video Visits Includes complete recording of video visits including the contact name and verified identity (with Telmate Verify).
- Focus with Filters Filter and sort by date, time, communication type, deposit and more.
- Deposits Time, place, amount and depositor details. With Telmate Verified, this includes photos and address information.
Connection Tool
Map Any Interaction Automatically
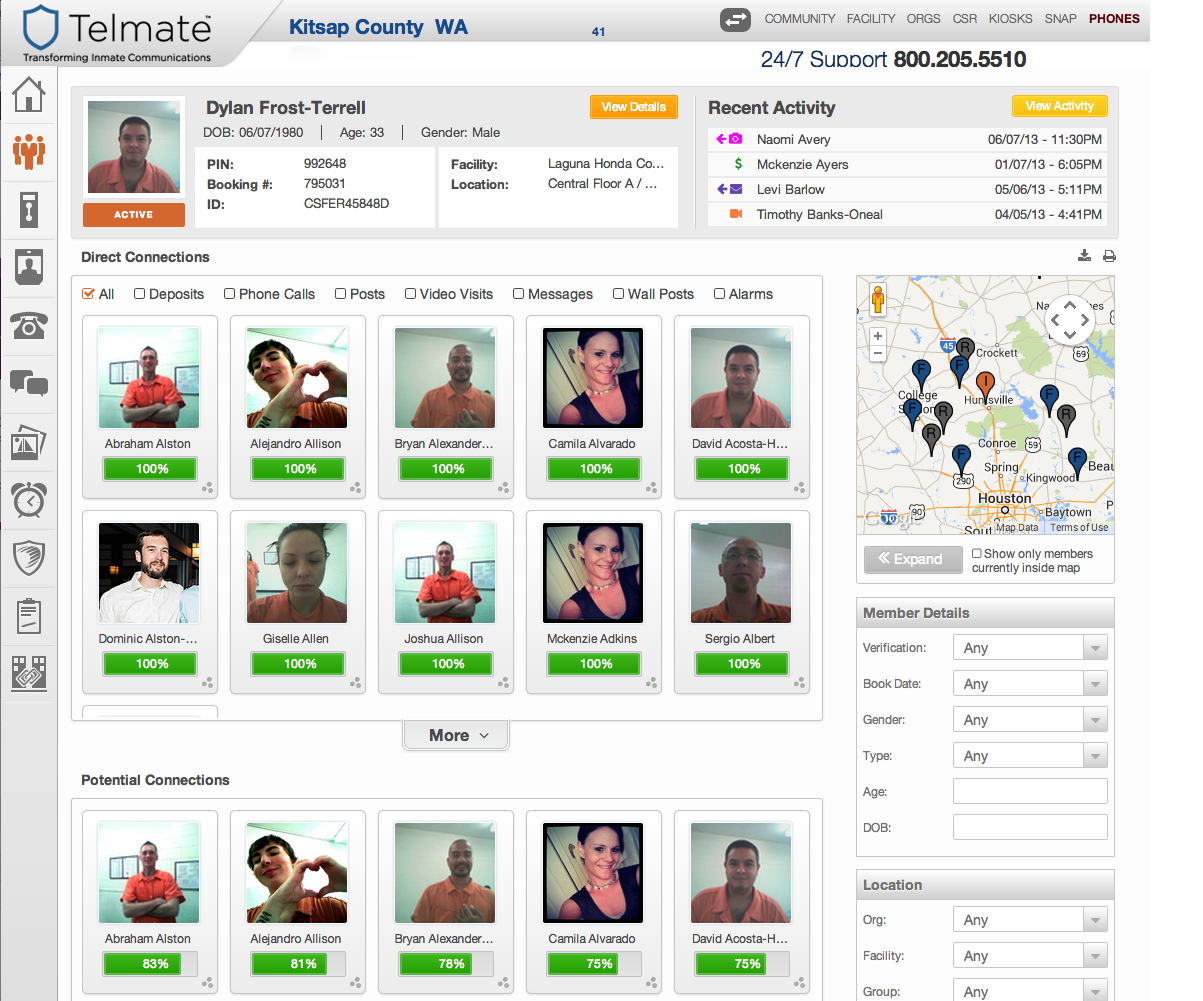
At Telmate we know that investigators spend a tremendous amount of time combing through visitation logs, phone records and financial deposit records to determine who your residents are in contact with.
Telmate has introduced a unique investigation tool that leverages the inmate’s communications activity with Telmate Verify to quickly and easily identify inmate personal networks and to highlight suspicious activity within those networks. Telmate Investigator can even suggest potential connections where direct contact has not been made. Your investigations will never be the same.
3-Way Call Handling
Telmate has the most comprehensive and accurate 3-way call detection system in the industry today. Most automated 3-way detection systems either disconnect (and possibly block) a large percentage of legitimate calls, or ignore a high number of 3-way events.
With Telmate, suspected 3-Way calls are: Automatically flagged as “3-Way Suspected” and a clickable timecode is provided to quickly link investigators to the point in the recording where a potential 3-way call was detected. Reviewed by live Telmate operators in less than 5 minutes to ensure accuracy and eliminate false positives. It takes one of our live operators less than 5 minutes from the time of detection to review a suspected 3-way call.
Voice & Image Biometrics
Telmate’s advanced and comprehensive image and voice biometric solutions verify the identity of every contact, measuring and analyzing unique physical and behavioral characteristics.
Image Biometrics: Do You Really Know Who is Visiting?
Security is a concern with every inmate interaction. When inmates conduct video visits, it is essential to ensure that the inmate that booked the visit is the one that conducts the visit, from start to finish.
With Telmate, every video visit is comprehensively analyzed for rule violations, including communications from unauthorized inmates. The Telmate system actively analyzes every video visit, comparing every face with a known and verified photo of the approved participants. When a mismatch is identified, the Telmate system instantly compares the unrecognized facial image with other verified inmate photos housed in the same location in an attempt to identify the unauthorized inmate participant. Next, Telmate timestamps any identified violation in the video and flags the live video visit for immediate review by facility investigators, along with a shortcut link that allows staff to quickly jump to and review the suspicious section of video and see the potential identity of the perpetrator.
Voice Biometrics: To Telmate, Every Inmate’s Voice is Like a Fingerprint.
Every human voice carries with it a unique set of characteristics. Each voice reflects acoustic patterns defined by the speaker’s anatomy, such as the size and shape of their mouth, nasal cavity and throat, and environmental (learned) patterns, such as accent, pitch, speed and cadence. Telmate can take each inmate’s voice, and use it in the following ways: